Presentation Attack Detection (PAD): The Essentials
PAD technology is critical to today’s fight against fraud, friction, and customer churn.
A silent battle to secure identities is raging beneath the surface of our increasingly connected and technologically advanced digital world. For businesses navigating the intricate web of digital transactions and biometric checks, the challenge is clear: how do organizations stay one step ahead of fraudsters and their schemes?
The answer lies in implementing Presentation Attack Detection (PAD) technology.
The critical need for PAD today
In the ever-evolving realm of digital identity, fraud attacks against identity verification systems have become increasingly sophisticated. Cybercriminals use every tactic – from printed facial photos to prosthetic masks to fake identity documents – to beat their way into organizations’ CIAM/IAM systems.
In background (literally and figuratively), PAD has emerged as a reliable and secure defense against these spoof attacks (also called presentation attacks), ensuring that only genuine users access the accounts and services registered under their identities.
For businesses, the growth of fraud incidence and fraud technology isn’t just a matter of data integrity. It’s about preserving brand trust, ensuring user safety, and maintaining the security of PII (personally identifiable information).
In an age where a single data breach can lead to irrevocable brand damage, the significance of using PAD technology in an identity ecosystem – no matter what industry you’re in – can’t be overstated.
Presentation Attack Detection tech: a breakdown
At its core, PAD technology serves as the ultimate gatekeeper. Its primary function is to ensure that users present genuine, “live” biometric images and that they physically possess their identity documents. Whether it’s facial recognition, fingerprint scanning, voice recognition, or iris detection, PAD ensures that the biometric factor presented isn’t a replica or a ‘replay’ from a recorded source – also known as a deepfake.
However, for all its stringent checks, PAD isn’t about creating a digital fortress that’s impenetrable for all users – only the disingenuous ones. PAD technology is about creating a seamless, frictionless onboarding and account access experience that’s as user friendly as it is secure.
APCER & BPCER
But how do we measure the efficiency of such a crucial system? Enter APCER (Attack Presentation Classification Error Rate) and BPCER (Bona Fide Presentation Classification Error Rate). These metrics are the lifeblood of PAD performance evaluation and offer quantifiable insights into its efficacy.
APCER is a metric that deals with false negatives. It evaluates how often the PAD system fails to identify a spoof attempt when one is presented. A high APCER indicates that the system is permitting too many fraudulent access attempts.
BPCER is all about false positives. It assesses how frequently the PAD system incorrectly flags a genuine presentation as a spoof attack. A high BPCER means that genuine users might face hurdles while trying to access a system.
For organizations across industries, striking the right balance between APCER and BPCER is essential. Too much emphasis on one can inadvertently heighten the other, leading to a system that’s either too lax or too restrictive.
Biometrics
Biometrics, in essence, is based on statistical hypothesis testing, which involves forming a hypothesis and validating its accuracy. When applied to biometrics, this methodology discerns genuine users from potential threats.
There are two main types of biometric factors: physical and behavioral (which includes device-based). Sophisticated biometric systems employ further layers of security, such as encryption, making it extremely challenging for unauthorized parties to misuse the data.
Physical biometric factors include: finger, palm, and voice prints; facial, retina, and iris scans; and hand geometry. Physical biometrics can’t be stolen, lost, forgotten, or reverse engineered by fraudsters. Facial biometric systems, for example, function by converting a facial image into a mathematical representation, or template. This template is a complex set of data points that represent unique facial features. The template creation process is one-way, meaning the original image cannot be reconstructed from the template. Even if a bad actor gains access to the stored template, they cannot reverse engineer it to recreate the original facial image or use it to directly attack an online system.
Behavioral biometrics are uniquely measurable patterns in a variety of human activities, from typing on a keyboard to swiping between screens on a mobile device to simply walking (gait). Behavioral monitoring, which can take place on two main platforms – keyboard and mouse or mobile device – is nearly invisible for customers and employees, who simply perform the measurable activities as usual.
Keyboard and mouse analytics can measure dwell time, key-to-key, total time to type, and mouse movements. On mobile, behavioral biometrics can leverage the chipsets embedded in a device to measure dwell, flight time, exchange, globularity, intensity, reactive shift, XYZ force, and XYZ motion. Because it can operate in the background of a web or mobile session, behavioral biometrics can enable continuous identity monitoring, which reduces the opportunity for criminals to take over a legitimate session. AI and machine learning analyze these patterns and create measurable data that can be used to verify and authenticate identity.
The two primary use cases for biometrics in digital identity are identification (also known as proofing and verification) and authentication.
Identification involves scanning a vast database to match an unknown entity, like an unidentified fingerprint at a crime scene.
Authentication is a process that ensures an individual is who they claim to be by using their unique biometric data.
These two processes, while fundamental, view biometric matches differently. For identification, a match can signal a potential threat; during authentication, a non-match might indicate an impersonator. Businesses must understand this distinction to choose the right biometric approach for their specific needs.
DET Curves
Visual aids like Detection Error Tradeoff (DET) curves offer a more intuitive understanding of PAD’s performance. These curves graphically represent false positives against false negatives.
Interpreting these curves can be instrumental in assessing how a company’s PAD system is faring and where improvements might be needed.
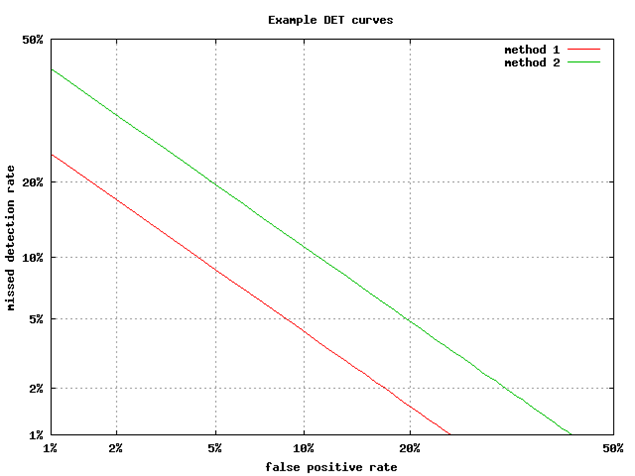
DET curves visualize the trade-off between APCER and BPCER. By analyzing these curves, businesses can optimize their systems to achieve the desired balance between security and user convenience.
Why PAD matters
As tech organizations and service providers across the globe expand the digital horizon, our reliance on secure, efficient, and user-centric identity verification systems isn’t just a necessity: it’s the very bedrock of each and every digital interaction.
Presentation Attack Detection technology, with its multifaceted layers of verification, AI-powered algorithms, and biometrics-based defenses, represents a roadmap for businesses to use in the fight against fraud.
However, embracing PAD isn’t just about building digital barriers. Implementing PAD requires businesses to strike a strategic balance between fostering unwavering user trust, cultivating lasting brand loyalty, and creating a future where digital engagements aren’t just efficient but inherently secure.
In a dynamic digital era, where threats shift and change with alarming speed, being merely informed is passé. Today’s security and business executives need to anticipate, prepare, and continuously evolve their organization for whatever comes next.
Why Daon?
With 20 years of experience in the identity assurance and biometrics industry, and an arsenal of AI-powered algorithms, Daon is committed to perfecting and constantly improving its innovative PAD technology. We currently have multiple novel patents either approved or pending approval for both image and document liveness detection.
When you choose Daon, you are choosing a true identity partner – not just a provider. And with the power of PAD from Daon on its side, your business isn’t just a passive spectator of the changing digital landscape – it’s an active architect of a digital future.
Learn how Daon can help you futureproof your identity ecosystem for whatever comes next.