Identity Verification vs. Authentication 101
You may have heard of identification, verification, and authentication...but what are some of the important differences between them?
Identity fraud cost consumers $12.5 billion in 2024 with 38% of fraud reporters losing money, making it critical for businesses to understand the distinction between identity verification (confirming someone is who they claim during account opening through identification and document validation) and authentication (validating established credentials when returning to access accounts). While verification happens once during digital onboarding using government-issued documents, liveness detection, and database checks to establish customer identities, authentication occurs repeatedly throughout customer relationships using passwords, biometrics, or multi-factor methods that balance security against account takeover attacks with the user experience demands of an increasingly competitive digital landscape.
Table of Contents
What is Identification?
What is Verification?
What is Authentication?
Identification vs. Verification vs. Authentication
The Power of Three: Identity Continuity
Cybercriminals are constantly finding new ways to attack businesses, and identity fraud remains one of their most frequently used methods. They obtain user credentials through various channels, with data breaches serving as a primary source. According to the Federal Trade Commission’s Consumer Sentinel Network, 6.5 million reports were filed in 2024, including more than 1.1 million identity theft reports.
Fraudsters put stolen information and credentials to work by attempting to convince businesses that they are legitimate customers, sometimes attempting to take over real customer accounts. The FTC reports that consumers lost more than $12.5 billion to fraud in 2024—a 25% increase over the prior year. What’s particularly concerning is that 38% of people who reported fraud in 2024 lost money, up significantly from 27% in 2023. The Insurance Information Institute notes that credit card fraud alone accounted for 43.9% of all identity theft cases.
The velocity and sophistication of attacks continue accelerating. The FBI’s Internet Crime Complaint Center recorded 859,532 cybercrime complaints in 2024, with potential losses totaling $16.6 billion. Investment scams led all fraud categories with $5.7 billion in reported losses, followed by imposter scams at $2.95 billion. Particularly troubling is the growth in job and employment scams, which jumped from $90 million in reported losses in 2020 to $501 million in 2024. As organizations adapt, authentication itself is evolving beyond simple point-in-time checks toward continuous verification models that maintain awareness of who is accessing services throughout an entire session.
The FTC warns: “We saw identity fraud-related crimes climb, particularly in attacks where cybercriminals impersonate someone to open accounts using stolen personal information to bypass security features.”
In a digital world fraught with scammers and schemes, it’s more important than ever for businesses in all industries to be able to know their customer (KYC)—to know, in other words, without a doubt that the person opening an account or returning later to access it is really who they claim to be.
-
What is the difference between identity verification and authentication?
Identity verification confirms someone is who they claim during account opening using documents, liveness detection, and database checks—happening once during onboarding. Authentication validates established credentials (passwords, biometrics, MFA) when customers return to access accounts, occurring repeatedly throughout relationships. With consumers losing $12.5 billion to fraud in 2024, understanding this distinction helps organizations balance security against account takeovers with user experience.
-
What is identification and how is it used in the identity process?
Identification is claiming an identity and providing evidence during account opening. Customers provide identifying information (name, address, email, SSN) and evidence like scanned driver’s licenses or selfies. Similar to MFA, users complete additional steps offering identity proof. Identification and verification are technically part of the same process but understood as two distinct steps during digital onboarding.
-
How does verification work to establish customer identity?
Verification checks identity proof against customer information, third-party data, and government databases to establish persons exist with histories matching provided information. NFC technology in government documents contains embedded chips with customer data and issuing authority signatures. Identity proofing platforms read chips confirming document details match chip contents. Selfies are checked for liveness detection protecting against fraudsters using photos or videos. Once complete, customers establish credentials for future authentication.
-
What role does liveness detection play in identity verification?
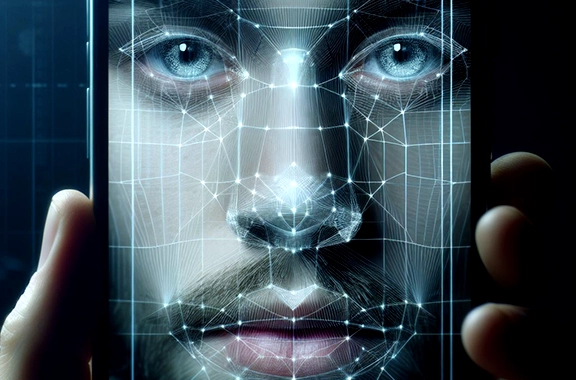
Liveness detection ensures selfies come from live persons rather than photos, videos, or deepfakes. The technology analyzes imperceptible details like light interaction with skin and micro-expressions that synthetic representations cannot replicate. By incorporating liveness detection, businesses ensure data comes from real documents and live persons, preventing synthetic identities and stolen credentials from bypassing verification during account opening.
-
What authentication methods do businesses use to balance security and user experience?
Simple authentication (username/password) is convenient but insecure. Biometric factors (fingerprints, facial scans) are nearly impossible to steal or replicate. Multi-factor authentication (MFA) requires identity factors plus codes sent to mobile phones, increasing security since criminals who steal passwords unlikely possess devices. Organizations balance security sophistication with convenience while protecting against $12.5 billion in annual fraud losses.
Let’s look at three terms which comprise the two separate processes that are critical to ensuring someone is who they say they are: identification, verification, and authentication. These terms are often used interchangeably, but they are distinctly different.
What is Identification?
According to Merriam-Webster, identification is “a: the act of identifying; the state of being identified, b: evidence of identity.”
In the physical world, when people are face-to-face, identification is relatively simple; recognizing a friend across the room is a no-brainer. Even when people aren’t face-to-face, the evidence of identity can be as low-key as when someone calls and says, “Hi, it’s Sam Jones.” For more formal and secure identification, government-issued documents such as driver’s licenses, identity cards, and passports are typically used. These same documents can also be used for identification in the digital world.
How Identification is Used
In terms of the identity verification and authentication process, identification occurs first, during verification.
A customer who wants to open an account online is asked for identifying information, such as their name, address, email, or social security number.
For increased security during the account opening process (also called digital onboarding), the customer may also be asked to provide evidence of their identity. As an example, they may be asked to use their mobile phone to scan their driver’s license.
Similar to MFA, the user is prompted to go through another step to offer evidence of their identity, such as taking and sharing a selfie after they have uploaded their driver’s license (read more about this below) Identification and verification are, technically speaking, part of the same process—identity verification—but are more easily understood when thought of as having these two steps.
What is Verification?
Merriam-Webster says verification is “the act or process of verifying.” It defines verify as “to establish the truth, accuracy, or reality of.”
Once a customer opening an account has submitted the information or documents required to establish their identity, the business uses verification, also known as identity verification, to ensure the customer is really who they claim to be.
How Verification is Used
At the most basic level, verification checks the proffered proof of identity (the driver’s license, passport, etc. chosen during the identification step) against known information about that customer, such as the selfie they took, as well as any relevant third-party and government databases, to establish that the person both exists and has a history that matches the information they’ve provided.
Verification has become easier and more secure as innovations in the IAM (identity access and management) industry have become more widely adopted; government-issued documents, for example, have become more sophisticated through the incorporation of technology such like near-field communication (NFC). With NFC, a chip embedded in the identity document contains both information on the customer and a signature from the issuing authority that proves the document is genuine. An organization’s identity proofing platform reads the chip and confirms that the details on the document match those contained within the chip.
When a selfie has also been requested from the customer, it is checked for “liveness.” Liveness detection protects against a fraudster trying to pass off a still photo or a video capture as the user’s genuine selfie.
Once verification is complete and the customer is confirmed to be who they say they are, they can establish the credentials they will use to authenticate themselves when they return to access their new account.
What is Authentication?
The Merriam-Webster online dictionary defines authentication as “an act, process, or method of showing something (such as an identity, piece of art, or a financial transaction) to be real, true, or genuine.”
In the digital identity world, it’s the key security step between someone presenting credentials they’ve previously established and being granted access to their account or data.
How Authentication is Used
Authentication is where the tension between needing to secure accounts against identity fraud and providing easy access for customersplays out. What does a customer have to do to authenticate themselves each time they want to access their account?
Authentication may be as simple as confirming that the customer has entered the correct username and password to be granted account access. It’s pretty easy for the customer, but it’s not very secure for them (or the organization).
The customer could also be asked to provide a more sophisticated identity factor, such as a fingerprint, facial scan, or other biometric factor. Biometrics provides an advantage over passwords because these factors are nearly impossible to steal or replicate
Businesses can also use multi-factor authentication (MFA) to decrease the likelihood of an ATO. A common example of MFA is when a customer enters their identity factor and is also asked to enter a four- or six-digit code that has been sent to their mobile phone. MFA increases security because it’s unlikely for a criminal who may have stolen the customer’s password to also physically possess the customer’s mobile device.
Identification vs. Verification vs. Authentication
While these three terms are interrelated, the two processes they are part of (proofing and authentication) are different in scope, purpose, how often they’re performed, and where they occur in the customer’s identity journey with a business.
Let’s take a closer look.
| Authentication | Identification | Verification | |
| What is it? | The act of authenticating a customer’s identity based on the established credentials they provide in an attempt to gain access to their account. | The act of a new customer claiming an identity. The first step in the verification process. | The act of verifying a claimed identity against other known sources to establish that the customer is who they claim to be before allowing them to open an account or to onboard. |
| Is the customer already known? | Yes | No | No |
| Is the process performed more than once? | Yes | No | Not usually. An exception may be if an existing customer opens an additional account. |
| Who initiates the process? | The customer | The customer | The business |
| What’s the result of the process? | If the customer has entered the correct credentials, access is granted to their account. | The business verifies the customer identity. | Once the business has verified their identity, the customer is allowed to onboard and establish the credentials they will use to authenticate themselves when they return to the account. |
The Power of Three: Identity Continuity
The proof of identity a customer is asked to provide to open an account (identification), how that proof is verified when the customer is onboarded (verification/proofing), and the sophistication of the credentials a customer must enter to gain access to their account during future authentications all determine an organization’s balance between security and UX. This can be a tricky equation: making accounts secure enough to deter fraudsters while also making them convenient for customers to access is a constant challenge for businesses in an increasingly competitive digital landscape.
Daon’s Identity Continuity platform, IdentityX®, combines the power of identity verification and authentication to help you define, deploy, and continually optimize a successful, seamless, and simple digital identity solution that fits the unique needs of your organization and its customers. Learn more by contacting us today.